Warning: I am not a software security expert. Please do not use this blog post as the basis for protecting highly sensitive code.
This past week I presented twice at SolidWorks World 2017 on SolidWorks API topics. In my first presentation, I demonstrated and discussed the pros and cons between macros, addins, and stand-alone programs as well as the common languages used to write each of them (VBA, VB.NET, and C#). One of the angles I considered was security. How can one protect their source code from being pirated or cracked? While this question isn’t about SolidWorks API per se, it is pondered often enough by API developers that I want to discuss it more detail.
Overview
With VBA macros, you only have one option: use the built-in password feature that will allow users to run the macro but not edit it. The problem is, this only stops people from viewing the source code. It does not stop anyone from using the macro. Moreover, with a little effort, one can replace the unknown password with a known password using a hex editor.
With .NET assemblies (e.g., the DLL or EXE that is built from your code), you have the option of implementing some form of licensing or password mechanism. This has two problems, however. First, as the licensing / password mechanism becomes more secure, it also tends to become more tedious for the user. (For example, if the licensing mechanism ties the user’s license to a particular machine.) Second, with some effort, the .NET assembly can be decompiled and then recompiled without the licensing mechanism.
While it isn’t possible to prevent decompilation (which is easily performed using a program like DotPeek and .NET Reflector), it is possible to obfuscate the source code in your assembly so that, even if it does get decompiled, understanding what your code does becomes difficult. Consequently, whatever security mechanism you have in place might be very tedious to remove.
Keep in mind: any client-side software can be pirated / cracked with enough time and effort. The only way to totally secure your source code is to never give your assemblies (i.e., your DLLs or EXEs) to anyone and instead use a Software-As-A-Service (SaaS) business model, in which case your assemblies will reside only on your server and your development machine. But SaaS isn’t even an option for many businesses.
A Change of Attitude
Trying to constantly stay one step ahead of pirates is usually futile. As one person on StackOverflow brilliantly put it, “It only takes one person cracking your code for it to be available to everyone. You have to be lucky every time. The pirates only have to be lucky once.”
More than just being futile, however, it can actually be bad for your business. The time and effort you put into securing your code does nothing to actually improve the user’s experience with your software. Indeed, if your security measures are cumbersome for the user to jump through, it can actually hurt their experience.
Consequently, the best deterrent to piracy may be to regularly improve your software and provide awesome customer service. As a result, the potential customer sees that the value you provide is worth the price they pay. They must believe that they will actually lose out by simply going with a pirated version of your software.
Another point to keep in mind is that if you’re selling business-to-business, the people who are going to use pirated copies of your software probably would not buy your software even if it were un-crackable. Therefore, I’m not convinced that in the B2B sphere, piracy actually results in that much loss of sales. If anything, piracy helps spread the word regarding your product and encourages you to focus harder on running a great business.
Anti-Piracy Measures Considered
Now, just because I think attitude is the most important measure you can take against piracy doesn’t mean its the only measure I think you should take. I think any program worth protecting ought to take these two measures:
- Licensing or password protection.
- Obfuscation.
Licensing / password protection simply means that your program requires some license key or password in order to operate. That way, pirates can’t simply copy your program and run it without any restrictions. But here’s the interesting part: the complexity or robustness of this mechanism is meaningless if pirates can simply decompile your program, remove the security mechanism, and then recompile it. This is always the case for programs given to the client. For example, consider this VB.NET program:
Imports System.Windows.Forms
Module Main
Sub Main()
Dim password As String = InputBox("Please enter the password.")
If VerifyPassword(password) Then
DoTheWork()
Else
MessageBox.Show("Sorry, wrong password.")
End If
End Sub
Private Function VerifyPassword(password As String) As Boolean
If password = "super secret password" Then
Return True
Else
Return False
End If
End Function
Private Sub DoTheWork()
MessageBox.Show("Running program...")
End Sub
End Module
The VerifyPassword() function is very simple. It tests to see if the user’s input string is identical to a hard-coded string. But what if this function was vastly more complex? It doesn’t matter because a pirate could simply decompile your code and modify Main() to include DoTheWork() and nothing else. The security mechanism would be completely bypassed.
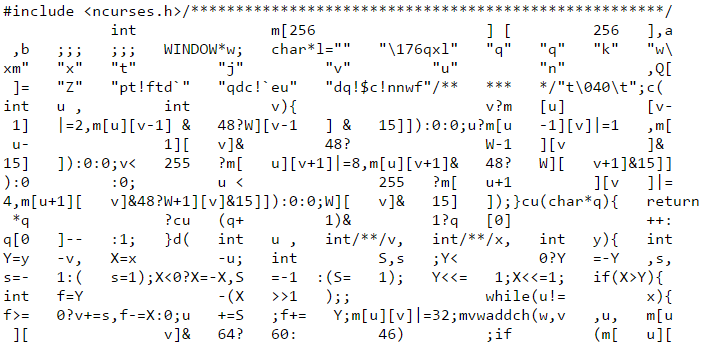
Enter obfuscation. Obfuscation is “the action of making something obscure, unclear, or unintelligible”. We can use a code obfuscator to make our code very hard to read and understand by scrambling our code’s metadata so that the normal namespace, variable, and method names are replaced by extremely short and unhelpful names. You can see an example here. The result is simply that your code is much harder to reverse engineer.
Implementing the Anti-Piracy Measures
If you think that piracy could adversely affect your business, it is worth implementing some simple security measures to at least make piracy very tedious. I’m going to show you, therefore, the simple password mechanism and obfuscation tool I use with some of my programs. Look at these measures as the “biggest bang for your buck” because it will cost you nothing but 30-60 minutes of your time.
Password Mechanism
Earlier I showed a password mechanism in which the user simply enters a string and it is compared to a hardcoded string in the program. That’s a bit too simple and I think someone who decompiled our program could figure out pretty quickly what the password is. I would rather implement a password mechanism that is robust enough that the pirate is forced to modify and recompile our code if they want to bypass the security mechanism. (Again, my aim is to reduce piracy by making it tedious to do.)
We could get a little fancier with our string password using a cipher, which is an algorithm that will convert the user’s input password into something more cryptic. For example, let’s say that the password to our program is “hello”. Rather than hardcoding “hello”, we’ll hardcode “rcoeoqppvxlcvdkeyacd”, which was obtained by the following algorithm:
1. Convert each letter in the string to the 10th letter ahead of that letter. (“hello” –> “rovvy”)
2. Insert three random letters at the end of each of the letters obtained in the previous step.
The disadvantage of this approach is that the pirate could still take the time to study the algorithm after they decompiled the program and thereby discover that the password is “hello”. The pirate probably wouldn’t; they would probably just recompile the code without the security mechanism, but if we implement an even more robust password mechanism, we can at least force them to go the recompilation route.
The more robust mechanism I am thinking of involves the difficulty of factoring extremely large semiprimes. A semiprime is the product of two prime numbers. Currently, the technology for factoring a 1024 bit semiprime in a reasonable amount of time does not exist. Therefore, we will hardcode a very large semiprime into our program. The password the user enters will be divided into this semiprime. If the remainder is zero and the password entered isn’t the semiprime itself, one, or zero, then the program is unlocked.
What I described above is known as asymmetric or public key cryptography. It is the basis for most of the common encryption algorithms, such as RSA. When used, the pirate has no realistic way to determine the public key (the password), which means that they are forced to decompile, remove the security mechanism entirely, and then recompile if they want to pirate the software.
To accomplish this, we need to first generate some really large prime numbers. In our case, we’re interested in two 512 bit primes that we can multiply to get a 1024 bit semiprime. The fastest way to do this, I have found, is through WolframAlpha using the RandomPrime[2*512] function. Using this twice, I get these values:
1030036602598976432683876090384311619779817426568199635721909308334853846166282705348098491480965944058167494832551044953489873701037371663414513077893831
3470286731786319967697161150108216266467687635597343214439309083506091064461655902744916175294419695183449301769152696093634596665123123708757988896620687
We need to get the product of these two numbers. If you try to do this in .NET using double or ulong data types, you’ll run into problems because these types aren’t designed to handle numbers of this size. Instead we have to use System.Numerics.BigInteger class, which has methods for performing calculations with very large integers, such as BigInteger.Multiply(). Using that method for the above primes will produce this semiprime:
3574522355253486376607090679412058587605209637050288224651312594499415157606938016760090741648625564943457074837124758850059987557386762219300792006878464303045773124661517310657808537475286266496854670334149759621269093438046706289243962191687054489020476430544359972981836807607429766985418843679264281897
Now, below is what a simple program that uses one of the prime factors as a password would look like. Don’t forget to add a reference to System.Numerics.
Imports System.Numerics
Class Program
Private Shared Sub Main(args As String())
Dim enteredPassword As String = Console.ReadLine()
If VerifyPassword(enteredPassword) Then
Console.WriteLine("Correct password.")
Else
Console.WriteLine("Incorrect password.")
End If
Console.ReadKey()
End Sub
Private Shared Function VerifyPassword(enteredPassword As String) As Boolean
Dim semiprime As BigInteger = BigInteger.Parse("YOUR SEMIPRIME HERE")
If BigInteger.TryParse(enteredPassword, Nothing) = False Then Return False
Dim divisor As BigInteger = BigInteger.Parse(enteredPassword)
If divisor = semiprime Or divisor = 1 Or divisor = 0 Then Return False
Dim remainder As BigInteger
BigInteger.DivRem(semiprime, divisor, remainder)
If remainder = 0 Then Return True Else Return False
End Function
End Class
A few final considerations:
- A password mechanism can be used with DLLs as well. You can have an internal / Friend boolean variable called “unlocked”, for example, that must be true before the public functions in your DLL can be used.
- One advantage of the cipher approach over the factorization approach is that with a cipher you can allow for multiple possibly keys, and generate a separate key for each of your users. That way, if a key / password finds itself into the wild, you can at least trace it back to a particular user, for whatever that is worth.
Obfuscation
I’m going to show you how to use a free, open-source obfuscator called Obfuscar. It is not the most convenient obfuscator to use, nor is it especially powerful, but it is free. Check out Eazfuscator.NET and Dotfuscator if you want a more robust, paid obfuscator.
Obfuscar is obtained as as NuGet package. NuGet is a tool created by Microsoft that lets you easily add external libraries to your project. (It’s not used for necessity, but for convenience.)
- Open your project in Visual Studio
- Right click on the project that you want to obfuscate and choose Manage NuGet Packages
- Click Browse and search for Obfuscar
- Select it and click the Install button
- Create an XML file to your project folder called “obfuscar.xml” (technically, the name is arbitrary) with this text:
<?xml version='1.0'?>
<Obfuscator>
<Var name="InPath" value="PATH TO YOUR BUILD FOLDER" />
<Var name="OutPath" value="PATH TO YOUR BUILD FOLDER\Obfuscated" />
<Module file="$(InPath)\MyAddin.dll" />
</Obfuscator> - Edit the XML file to include your actual build folder (wherever the DLL / EXE is built to). If you have multiple DLLs / EXEs to build then you can have multiple Module nodes.
- Locate Obfuscar.Console.exe, which will be in a solution folder called “packages”.
- Run this executable from the command prompt with the path to obfuscar.xml as the argument.
- The obfuscated assembly will be located in your build folder in a subfolder called Obfuscated.
Note: Signed assemblies will not work after obfuscation with Obfuscar and must be resigned. Instructions on how to have Obfuscar sign your assembly post-obfuscation are here.
Additional Reading On Software Security
<> Obfuscating Code. Discusses the transparency of .NET assemblies and why obfuscation is essential for protecting software written in .NET.
<> Other ideas for protecting DLLs from being referenced: Here and here and here. The last one lists obfuscation and asymmetric cryptography as the first defenses and also explains the importance of focusing on building better software that customers want to pay for, versus obsessing over thwarting people who would never buy your software in the first place.
<> Security through obscurity – Is SolidWorks API-related code “safer” just because the SolidWorks API is not widely known of or used? It depends on what you’re trying to prevent. If you’re trying to prevent someone from using your assembly, no. If you’re trying to prevent someone from repurposing your code, probably.
Conclusion
Every developer has to consider the threat of piracy and then make a business decision on what amount of security is worth implementing. No client-side assembly can be completely safe, therefore it is important to know when “enough is enough”. Sometimes, the best anti-piracy measure is to add enough value through subscription or customer service that users aren’t tempted to use pirated versions of your software.
Most of the software I write is used internally by my customers, therefore piracy is not even on the radar. If you have experience writing software that is sold more publicly then I would be interested in your preferences regarding software security.
Keith
Want to stay up-to-date with new CADSharp content, including new videos, blog posts, and training opportunities? Join our newsletter.

Leave A Comment
You must be logged in to post a comment.